BIOMETRIX WEBLOG: BIOMETRIC AUTHENTICATION TECHNOLOGIES
A personal weblog on issues related to the use of biometrics, in order to promote the effective development & implementation of all Biometric technologies (Fingerprint, Iris, Retina, Voice Recognition, Vein, Hand, Keystroke dynamics, Signature) standards and applications.
Wednesday, January 02, 2008
Friday, March 24, 2006
WiMAX arrives in London
The company's Web site estimates the value of the free installation, hardware and three months free trial at £1,353 and says subscribers have no obligation to continue at the end of the trial. Urban WiMAX expects to offer a two-year contract, with no installation fee. We note that the company does not reveal what vendor it is using for the gear it offers. We also note that the company is serious: Its Web site includes an advanced postal zip code checker, which takes into account hills, trees and contour lines in order to include line-of-sight connection. Techworld Mobility reports that its office on Brixton Hill passed the test (they can see the London Eye from their roof).
For more on Urban WiMAX London trial
Al Rajhi Bank deploys biometric ATMs
Al Rajhi Bank deploys biometric ATMs
21st March 2006
Saudi Arabia's Al Rajhi Bank has struck a deal with Diebold, a self-service and security systems provider, for the provision of its self-service biometric automated teller machines (ATMs). Diebold's biometric Opteva ATMs will be deployed at social security offices throughout Saudi Arabia, where 400,000 retirees will use the unique geometry of the index finger in conjunction with a magnetic stripe card to access monthly retirement payments. The biometric technology replaces the use of personal identification numbers (PINs) with authentication of identity. Diebold Professional Services will manage the implementation of 82 biometric terminals, providing overall development of the biometric software solution, and will create a customized user interface in the local language. Suliman Al Obaid, general manager of IT at Al Rajhi Bank, said: "Diebold's biometric ATMs will allow us to expand our business by distributing government-mandated pension payments on a monthly basis. Our biometric program may be expanded to include the enrolment of other customers in rural areas who are unfamiliar with the use of PINs."
Thursday, March 23, 2006
Conferences 2006
· SPIE Biometric Technology for Human Identification III, April 17-21, 2006, Orlando, Florida
http://spie.org/Conferences/Calls/06/dss/conferences/index.cfm?fuseaction=OR36
· 3rd Summer School for Advanced Studies on Biometrics for Secure Authentication, June 5–9, 2006, Alghero, Italy.
http://www.computer-vision.191.it/Biomet-School.html
· ICPR 2006, August 20-24, 2006, Hong Kong.
http://www.comp.hkbu.edu.hk/~icpr06/
· IWMRCS 2006, September 11-13, 2006, Istanbul, Turkey.
http://www.ehb.itu.edu.tr/~mrcs
· Biometrics Symposium 2006, September 19-21, 2006, Baltimore, Maryland.
http://www.citer.wvu.edu/bsym2006/
· ICB 2007 August 27-29, 2007, Seoul, Korea
http://image.korea.ac.kr/ICB2007/index.html
Thursday, March 02, 2006
Email to Zayn007
Biometrics traits (physical) are unique, it was proven that even twins have unique fingerprints, irises, retinas, shape of ears, but no major applications so far like the one the UK govrnt is trying to launch with ID cards and passports, so that will be a huge challenge with a number of security issues, a centralised DB with millions of templates, you can imagine!. So to sum up, to verify 1 ID among millions, let's say 60 million (K population) has not been yet tried, so until they finally enrol every single citizen in the UK (60 million +), we wouldnt' know, I think most major pilot projects experimenting with biometrics have not yet exceeded 25,000-50,000 samples. The whole market is still maturing, technology is still under R&D, and the hype does help from bad publicity about big brother watching, and spoofing of biometric devices. Biometrics can be secure if used effectively with the traditional authentication methods (PIN, tokens, smart cards...) Secondly, every biometric has weaknesses and strenghts, you've mentioned "unique" that's one of the criteria of any biometric, if they are not unique, they won't be used as an authentication method. The problem is that what are going to do with disabled people with no eyes, no fingers, no hands. Each biometric technique is measured using different rates, namely False Rejection Rate (probability that a biometrics fails to verify & reject a legitimate user), False Acceptance Rate (probability that a biometrics system accepts an imposter), Equal Error Rate (occurs at the decision threshold where the proportion of false rejections equals the proportion of false acceptances).
They come up with a solution, using Multi-biometrics, for example this UK ID they're trying to do will include, face recognition, 10 fingerprints, 2 irises and signature, all saved in one chipped card, so if one trait do not match or is not on record, there is always an option of using another one. Templates are being updated each time there is a successful verification, because there is the problem of ageing, as we get older, it gets harder to get good Acceptance/rejection Rates.
I agree, the main concern with ID cards will be forgery, and biometrics alone will not prevent forgery or fraud. In Holland, they used strong encryption, but apparently Dutch biometric passports have already been hacked!!. See it's how you implement the technology, biometrics work in certain applications, but for a huge project like ID cards of millions of people, umm... (not too sure) but there are advantages, but biometrics have to be used as a layer on top of (smartcards, encryption or passwords) I think here in the UK, if they try to store the data as an algorithmic encryption, it will make it impossible for even the most sophisticated fraudster to read or substitute.another thing, why do they need to store our individual data on both card and central database? until now, We don't understand why they need to do this, i think they are planning to extend the usage of the cards in future, which will be a major concern for the civil liberty groups. Other countries such as France and Italy have stipulated that biometric information is stored only on the cards themselves - thus still within the possession of the individual. So why has the UK decided to include a central database as well? We can understand that from a security point of view, central storage makes the most sense in an online world. But if you're also storing this on the cards themselves, that invalidates the security argument. Another concern is, will the project work? The LSE has raised concerns about this and the government does not have a strong track record here.
bottom line, USA is dictating, they want biometrics, UK governmt will be issueing biometrics passports and ID cards sooner of later, because USA is saying so, security is not a priority, they have an excuse, "we have to fight terrorism" ...
Mobile virus jumps from PC to mobile device
http://news.com.com/Virus+makes+leap+from+PC+to+PDA/2100-1029_3-6044457.html?tag=nefd.top
UB Biometrics Researchers Enhance Fingerprint Technology
http://www.linuxelectrons.com/article.php/20060301003629550
Tuesday, February 28, 2006
NIST Issues Final Federal Biometric Specs Government Technology
http://csrc.nist.gov/piv-program/index.html
Thursday, January 05, 2006
Researchers pore over biometrics spoofing data
Published: Thursday 22 December 2005
Sweaty hands might make you unpopular as a dance partner but they could someday prevent hackers from getting into your bank account. Researchers at Clarkson University have found that fingerprint readers can be spoofed by fingerprint images lifted with Play-Doh or gelatine or a model of a finger moulded out of dental plaster. The group even assembled a collection of fingers cut from the hands of cadavers. In live fingers, perspiration starts around the pore and spreads along the ridges, creating a distinct signature of the process. In a systematic test of more than 60 of the carefully crafted samples, the researchers found that 90 per cent of the fakes could be passed off as the real thing. But when researchers enhanced the reader with an algorithm that looked for evidence of perspiration, the false-verification rate dropped to 10 per cent. The idea of using perspiration is promising as a way to beat hackers because sweating follows a pattern that can be modelled. In live fingers, perspiration starts around the pore and spreads along the ridges, creating a distinct signature of the process. The algorithm, created by Stephanie Schuckers, associate professor of electrical and computer engineering at Clarkson, detects and accounts for the pattern of perspiration when reading a fingerprint image. Dead fingers don't sweat. Schuckers said in a pre-released statement: "Since liveness detection is based on the recognition of physiological activities as signs of life, we hypothesised that fingerprint images from live fingers would show a specific changing moisture pattern due to perspiration but cadaver and spoof fingerprint images would not." The research, funded by a $3.1m grant from the National Security Agency and conducted in collaboration with other universities, is part of an ongoing effort to improve biometric authentication and identification. Other methods are in the works as well. Fingerprint readers essentially take a picture of a fingerprint and match it to a sample in the database. To get around spoofs involving lifted fingerprints, NEC researchers have developed technology that actually takes a picture of the tissue underneath the fingertip to get a three-dimensional image that can be matched against a database sample. Fujitsu has developed an authentication technology that looks at vein patterns. Although biometric identification technologies continue to improve, each has its own flaws. Voice authentication is fairly accurate and tough to spoof, say advocates, but it can be affected by a bad phone connection. Iris scans work well but are commercially impracticable. Face scanning is actually less accurate than most but consultants for the US State Department say the technology was chosen for electronic passports because that particular identity test seems to make people feel less like criminals. Michael Kanellos writes for CNET News.com http://software.silicon.com/security/0,39024655,39155244,00.htm
Thursday, September 22, 2005
Biometric Myths
by Russ Davis
CEO of ISL Biometrics - Tuesday, 13 July 2004.
It is probably the hottest sector in the security field today. Yet the biometrics industry, which produces human-based identification systems, is weighed down with claims and counterclaims, fallacies and myths. While some of the myths are no doubt based on an element of historical or scientific truth, some are now so out of date or inaccurate that they are almost laughable...
Monday, September 12, 2005
The BITE project

BITE aims to prompt research and to launch a public debate on bioethics of biometric technology. The number of biometric devices in use in Europe has jumped from 8,550 in 1996 to more than to 150,000 in 2004 and biometric industries revenues are expected to more than triple in the next two years. “Biometrics seem headed for dramatic growth in the next few years. But calm, public discussion of their benefits and drawbacks has been lamentably lacking” (The Economist, Prepare to be scanned, Monday December 8th 2003). The BITE project aims to launch such a discussion. The BITE project offers a unique combination of academic centres, industries and international organisations with the aim to help industry and researchers to confront ethical issues that arise in biometrics. The project is coordinated by Prof. Emilio Mordini, director of the Centre for Science, Society and Citizenship (Rome).
Wednesday, August 03, 2005
BANKS TO ESTABLISH ...
http://www.thebiometrix.com/viewtopic.php?t=377
Saturday, July 30, 2005
BIOMETRICS E-SYMPOSIUM 2005
Val-Pierre Genton
Biometrics E-Symposium
Chair vpg@e-symposium.com
T. +44 (0)20 7613 0800
Wednesday, July 20, 2005
EARS RECOMMENDED FOR BIOMETRICS
http://www.thebiometrix.com/viewtopic.php?t=368
Friday, July 08, 2005
Universal Biometric ID (UBID) system
http://www.thebiometrix.com/viewtopic.php?t=326

Thursday, July 07, 2005
LONDON'S HOUR OF HELL 7 7 2005
 I was travelling into work this morning, and I normally travel on the Central Line to Tottenham Court Road and then walk to New Cavendish street, 10 minutes later, at 09:35am, on the way to work I found out what had happened and I couldn't believe I had just missed it and I am still in shock. I just thank God Almighty that I left late...
I was travelling into work this morning, and I normally travel on the Central Line to Tottenham Court Road and then walk to New Cavendish street, 10 minutes later, at 09:35am, on the way to work I found out what had happened and I couldn't believe I had just missed it and I am still in shock. I just thank God Almighty that I left late...The media coverage today was appalling, only late in the day was there any helpful advice for people trapped in the zone.
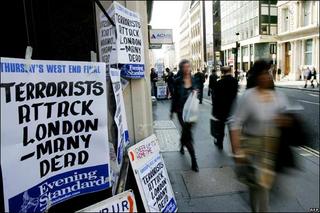
My thoughts are with those who were actually caught up in it all. I can only offer my prayers for the people of Great Britain right now, and most especially for the victims and their families. I am a Londoner and if there is a city who can withstand this senseless and futile form of terror, it is London and its residents. Today is a sad day in London and the world at large, the future is bright. Londoners, irrespective of faith, must continue as far as is possible with their every day lives. May God help those who have been affected by the attacks and guide us all towards creating a more peaceful world.
Saturday, July 02, 2005
VEIN SCAN BIOMETRIC
Friday, July 01, 2005
GENERAL DISCUSSION ON THE UK ID CARDS
Leading politicians, academics and IT experts warn that this project could turn into the biggest-ever government IT disaster. Are you for or against the ID card?
More articles and discussions in this forum: http://www.thebiometrix.com/viewforum.php?f=28
63% of consumers ...
63% of consumers would pay for biometrics if it provided additional security by ZDNet's ZDNet -- A survey of more than 2,000 adults, sponsored by AuthenTec, shows that 63% of consumers would pay extra to add fingerprint biometrics to their PC and notebook computers, while 71% would pay more for this feature in their cellular phones. Most consumers said they would use the technology to replace their PC and Internet passwords, [...]
Saturday, June 18, 2005
Thebiometrix.com Discussion Forum
http://www.thebiometrix.com
For a long time we have sensed an ever growing active community in the field of Biometric technologies, and here's a chance to engage in discussions generated from material on the forum. We are confident that vibrant discussions WILL take place and we hope that vitality WILL thrive here as well.
TheBIOMETRIX.COM was founded in mid January 2005 by a group of enthusiastic researchers & web developers from the UK, USA, Romania, Greece & Morocco.
TheBIOMETRIX.com welcomes your participation in our Discussion Forums. These forums offer you the chance to interact with researchers, experts, developers, analysts, consultants, students, vendors, the general public and with any other users.
We ask that you Post with respect for all fellow forum participants. This is a community, so when you post, we encourage you to tell your fellow community members a little about who you are - not just an e-mail address, but a bit of a bio. It enriches the discussion to know who's "behind the post."
Join http://theBIOMETRIX.COM discussion forum for free.
The forum is easy to use and has numerous helpful features, once you have registered you can check the FAQ section, where you can find answers for your questions and how theBIOMETRIX.com forum functions.
A special thank you to: Henry J. Boitel, Cristian Donciulescu, Yona Flink, Michael Cherry, Nikolaos Papamichael, Rachid Bencheikh, Bradley Malin, Bill Rogers for their valuable feedback and encouragements.
Many thanks
© Copyright 2005 TheBIOMETRIX.com
Monday, June 06, 2005
Your fingerprints are everywhere
How much do you trust your government? That's a question that all of us have to ask, perhaps the more often the better. Thomas Jefferson, one of the founders of the United States and its third President, wrote to Abigail Adams in 1787 sentences that may seem incredible to many people today:
"The spirit of resistance to government is so valuable on certain occasions, that I wish it to be always kept alive. It will often be exercised when wrong, but better so than not to be exercised at all. I like a little rebellion now and then. It is like a storm in the atmosphere."
One way to define a government is by whom it controls; in other words, governments serve to provide necessary services to their citizens, like roads and armies, but governments can also legally restrict your physical movements, your property, and your rights. That's why someone can sue you in civil court for money, but losing a civil suit cannot lead to your imprisonment or the loss of your civil rights. If you have the misfortune of being tried in criminal court, however, the state is your opponent, not an individual, and losing that trial can result in the loss of your freedoms of movement, property ownership, and civil rights...
http://www.securityfocus.com/columnists/333
links:
http://www.csmonitor.com/2005/0602/p01s04-ussc.html
http://www.boingboing.net/2005/04/28/thumbprinting_visito.html
http://www.naperville-lib.org/PDFfiles/Biometrics.pdf
http://www.ccc.de/biometrie/fingerabdruck_kopieren.xml?language=en
http://www.puttyworld.com/thinputdeffi.html
http://www.pcworld.com/news/article/0,aid,120112,00.asp
http://www.theregister.co.uk/2004/05/20/us_passports/
Thursday, May 26, 2005
IS BIOMETRICS ...?
By Dave Kearns
Network World Identity Management Newsletter, 01/26/05
http://www.nwfusion.com/newsletters/dir/2005/0124id2.html
Tuesday, April 19, 2005
DIGITAL IDENTITY
http://blog.onghome.com/2005/04/identity-ontology-taxonomy.html
A good contribution to existing concepts relating to identity management.
Saturday, April 09, 2005
MITSUBISHI INTRODUCES ...
New fingerprint reader scans prints without touching skin. The world's first scanning device that reads fingerprints without touching the skin will hit the market this autumn, Mitsubishi Electric said.
The device could be used to enhance security measures at financial institutions and airports.
The new scanner uses light from a red light-emitting diode (LED) to read fingerprint patterns under the surface of the skin. Red LEDs are typically used in a wide variety of industrial uses, such as in automotive electronics or medical instruments.
Ordinary fingerprint sensors take prints using physical contact between the finger and a glass plate.
In some cases, however, such physical fingerprint readers are unable to take an accurate print when the subject's skin is rough, wrinkled or covered in perspiration.
In the new LED device, the user places a finger in the reader with the nail facing up. A light scans through the finger and analyzes the convex and concave patterns of the skin layer below the surface.
Financial institutions, eager to find ways to circumvent thefts of personal data and cash, are anxious to find devices like the Mitsubishi Electric reader to provide better identification at ATMs.
Friday, April 08, 2005
IWWST 2005 LONDON UK
The 3rd International Workshop in Wireless Security Technologies aimed at bringing together academics and industry in an effort to further and enhance the interactions between researchers and promoters of wireless technology.
IWWST 2005 is organised by the Wireless Information Technology Research Center (WITRC), Cavendish School of Computing Science, University of Westminster, in collaboration with the British Computer Society - Wireless Information Technology Specialist Group. Keynote speakers were from HP Research Labs, Monmouth University (USA),Microsoft Research Cambridge (UK)
I presented a paper titled: "Hybrid Authentication Systems: Towards Robust User Authentication On Wireless and mobile Devices Using Biometric Technologies".
http://www.iwwst.org.uk
Saturday, April 02, 2005
UPCOMING CONFERENCES
http://biometrics.cse.msu.edu/avbpa2005.html
• National Academies "Whither Biometrics?" Workshop, March 15-16, 2005, Washington, D.C.
http://biometrics.cse.msu.edu/whitherbiometrics_workshop.htm
• Biometric Technology for Human Identification (OR31), March 28-April 1, 2005, Orlando, Florida.
http://biometrics.cse.msu.edu/spie-or31.pdf• SCIA 2005, June 19-June 22, Joensuu, Finland. http://www.cs.joensuu.fi/scia05/
• ICIAP 2005, September 6-8, 2005, Cagliari, Italy.
http://www.iciap2005.it/
• Biometrics Symposium 2005, September 19-21, 2005, Crystal City, VA.
http://www.citer.wvu.edu/bsym2005/
• ICBA 2006, Jan 5-Jan 7 2006, Hong Kong. http://www4.comp.polyu.edu.hk/~icba/
Tuesday, September 14, 2004
R. Bencheikh GETS a UK BIOMETRIC ID CARD

UKPS trial-Biometric ID card

The UK Passport Service (UKPS) is running a trial to test the recording and verification of the facial recognition, iris and fingerprint biometrics. I took part in the trial, and …
this is what I experienced at Globe House, 89 Eccleston Square,
London, SW1V 1PN.
It's a sunny summer afternoon and I'm sitting in the bustling main passport application waiting room in London. I'm here to enrol as one of the lucky 10,000 volunteers in the UK government's biometric ID card trial and check out the process for myself.
I was greeted in a reception area for enrolment, which consisted of filling out a form with basic information about myself such as gender, age, postcode and ethnic background.
A small side room, in the second floor, off the main waiting room contains a large booth with a curtain around it. Inside a chair sits in front of a desk with one machine that scans the iris and takes a facial biometric (Panasonic BM-ET300, http://www.raycosecurity.com/biometrics/iris.html ), and another machine that takes a fingerprint scan (Identix TouchPrint™ 3100 Live Scan, http://www.identix.com/products/pro_livescan_3100.html ). For good measure there is a screen to sign an electronic signature on.
The aim of the trial is to test the enrolment process for each of the different biometrics to see how easy they are and also test them for accuracy.
I'm ushered into the booth and took a seat in front of the camera, which sits at face height. First up is the facial recognition. I asked if I can smile, it was allowed! (http://news.com.com/E-passports+are+nothing+to+smile+about/2100-7348_3-5299928.html ).
Then I positioned my eyes so they are looking into the iris scanner. A computer voice prompt tells you to move closer or further away until you are in the right position and after some whirring and a couple of camera clicks, the iris scan is done.
The UKPS operator taking my scans says there have been none of the problems highlighted earlier this year by MPs from the Home Affairs Select Committee who claimed long eyelashes, watery eyes and eye complaints could render iris scanning useless for large numbers of the population.
She said the guides on the iris scanning machine and the computer voice prompt will ensure peoples' eyes are aligned correctly with the reader. And speaking as someone with long eyelashes I certainly didn't have any problems on the day.
Next up is the fingerprint scanner, the scanner was cleaned by the UKPS operator with a cloth. It looks much like a scaled-down version of a regular computer scanner with a glass screen. First you put your four left fingers on the screen, then the thumb, and repeat the process for the right hand.
The system enables the operator to check all the prints scanned are of a good enough quality to be used. Ones that aren't are highlighted and are simply taken again. Because all the fingers and thumbs are scanned it also isn't an issue for people with the odd digit missing.
Interestingly, The UKPS operator said that a database of one million fingerprint scans has been imported from abroad for use during the trial to ensure that there is a big enough volume to check how accurate the matching process is with the 10,000 prints taken during the trial.
After giving an electronic signature, volunteers will then be given a few minutes to fill out a questionnaire asking them about how they comfortable they felt using each of the biometrics and how intrusive they thought each was.
Less than 15 minutes after starting the biometric trial, the UKPS operator hands me my very own biometric ID card. It's only a demonstration one and can't be used anywhere but the chip on it does contain my biometrics. Volunteers then get to choose one of the biometrics so it can be tested against the card.
I opt for the iris scan. The card is put into a reader and I sit in front of the iris scanner again. A problem with the server connection means it doesn't register first time but a few seconds later I get a correct match. The process has been smooth and painless and taken quarter of an hour with all three biometrics. The UKPS is currently getting through about four people an hour.
Et voila! I had to finish my questionnaire, I was also assured that all the data collected during the trials will be completely destroyed at the end of it all.
No stats are yet available on the failure and success rates of the different biometrics but a full government report is due out later in the year after the trials finish.
As I was leaving the UKPS office, I heard a voice saying "We'll be tracking you young man …"
Friday, August 27, 2004
PREMIER HANDHELD ...
Judges at ISC West in Las Vegas, Nevada, in April were so impressed with Datastrip's DSVII-SC that they gave it the New Biometric Product of the Year award.
“The DSVII-SC is a new mobile device that was introduced in April, 2004,” said Melinda Morris, Datastrip’s inside sales manager at the company's corporate headquarters in Exton, Pennsylvania. “The devices are currently being used in the U.S. and worldwide by system integrators and Automated Fingerprint Identification System (AFIS) providers for solutions being developed for law enforcement, transportation, schools, prisons, nuclear power plants and other high security facilities.”
Friday, August 13, 2004
BIOMETRICS: A GRAND CHALLENGE
Reliable person recognition is an important problem in diverse businesses. Biometrics, recognition based on distinctive personal traits, has the potential to become an irreplaceable part of many identification systems. While successful in some niche markets, the biometrics technology has not yet delivered its promise of foolproof automatic human recognition.
Tuesday, August 10, 2004
THE UKPS BIOMETRICS ENROLMENT TRIAL
http://www.ukpa.gov.uk/news/news.asp?intElement=784
LIVENESS DETECTION IN FINGERPRINT RECOGNITION SYSTEMS
A good effort by Marie Sandström at Linköping University in Sweden, here is the abstract of her thesis.
Monday, August 09, 2004
THEORY OR REAL-WORLD TESTS
- A brief outline of Professor Daugman's paper.
- An email to the BC that I sent a year ago outlining a proposal forlayered biometrics.
- An article appearing in Wave this month.Combining Multiple Biometrics John Daugman, The Computer Laboratory, Cambridge University Overview This short note investigates the consequences of combining two or morebiometric tests of identity into an "enhanced" test.
There is a common and intuitive assumption that the combination of different tests must improve performance, because "surely more information is better than less information." On the other hand, a different intuition suggests that if astrong test is combined with a weaker test, the resulting decision environment is in a sense averaged, and the combined performance will lie somewhere between that of the two tests conducted individually (and hence will be degraded from the performance that would be obtained by relying solely on the stronger test). There is truth in both intuitions. The key to resolving the apparent paradoxis that when two tests are combined, one of the resulting error rates (False Accept or False Reject rate) becomes better than that of the stronger of thetwo tests, while the other error rate becomes worse even than that of the weaker of the tests. If the two biometric tests differ significantly in their power, and each operates at its own cross-over point, then combiningthem gives significantly worse performance than relying solely on the stronger biometric. Example: Combination of two hypothetical biometric tests, one stronger thanthe other: Suppose weak Biometric 1 operates with both of its error rates equal to 1 in 100, and suppose stronger Biometric 2 operates with both of its error ratesequal to 1 in 1,000. Thus if 100,000 verification tests are conducted with impostors and another 100,000 verification tests are conducted with authentics, Biometric 1 would make a total of 2,000 errors, whereas Biometric 2 would make a total of only 200 errors. But what happens if thetwo biometrics are combined to make an "enhanced" test? If the "OR" Rule is followed in the same batch of tests, the combined biometric would make 1,099 False Accepts and 1 False Reject, for a total of 1,100 errors. If instead the "AND" Rule is followed, the combined biometric would make 1,099 False Rejects and 1 False Accept, thus again producing atotal of 1,100 errors. Either method of combining the two biometric tests produces 5.5 times more errors than if the stronger of the two tests hadbeen used alone. Conclusion: A strong biometric is better alone than in combination with aweaker one... when both are operating at their cross-over points. To reap any benefits from combination, the equations above show that the operating point of theweaker biometric must be shifted to satisfy the following criteria: If the"OR" Rule is to be used, the False Accept rate of the weaker test must be made smaller than twice the cross-over error rate of the stronger test. If the "AND" Rule is to be used, the False Reject rate of the weaker test mustbe made smaller than twice the cross-over error rate of the stronger test. The following is a position I took on layered biometrics in an email about ayear ago to the List. I do not think that the below disproves ProfessorDaugman's premise, but only points out that the premise from which I andothers have based their conclusions are different from that of Professor Daugman.The idea of layered biometrics has come about because of False Rejection. The layered biometrics issue may therefore be approached from another pointof view by not layering the biometrics but subjectively comparing the statistical results. At first, this may sound very non-scientific, butlet's first examine the problem of FR. Let us take for our examination two widely used biometric technologies forAccess Control: Hand Geometry and Face. In our example, both these system will be used for an access control system. The Hand Geometry reader will beour primary biometric system with the Facial Verification being our secondary system. Hand Geometry has a field proven EER of 0.2%. For our example, we will set the Hand Geometry reader's security at a threshold level of 60 which gives us a FAR of 0.08%. What we are saying in essence is that any person that verifies at or below the threshold level of 60 is who heclaims and anyone over the threshold level of 60 is an imposter and will notbe granted access. If a person verifies at 61, how much more of an imposteris he than the person that verified at a threshold level of 59 or 60? And if that same person verified at 69 or 75, is he more of an imposter than theperson that verified at a threshold level of 40? From the stand point ofthe set threshold level, anyone above 60 is an imposter and anyone at 60 or below is not an imposter. When we set a threshold level, there is a clear YES or a NO and no 'possible'. In the real world, we know that people may not always verify at the same level day in and day out. Should we reject a legitimate user because theuser failed by 0.05% and was verified at 61 instead of the minimum threshold level of 60? There may be a case for 'parallel biometrics'. In the case of parallel biometrics, we state that any person that does not meet the minimum threshold level will be verified by a second biometric technology. In this case, Facial Verification will be used. Let us assume that two persons, George and Giles were verified at the Hand Geometry reader and George received a verification level of 65 ( FA% 0.11%) and Giles received a verification level of 85 (FA 0.28%. George came pretty close toour required FA% of 0.08%, but could not be allowed access because he missed the threshold level by 0.03%. Close but no prize. Now, George and Giles are given a second chance to prove that they are who they claim. Both George and Giles look at the camera and receive the following verification levels: George is verified at a FA level of 7 % and Giles at 3 %. In the Facial, Giles came out better than George. If we hadbeen using Facial Verification alone and our access control threshold had been set for 98%, neither George nor Giles would have gained access. But now we are using Facial Verification in parallel with Hand Geometry. George did better than Giles with Hand Geometry but Giles did better than George with Facial. Do we deny both access because the did not meet the facial minimum requirements or should be combine both the Hand Geometry and Facial and divide by 2 or just toss a coin? Or should we ask an additional question: What is the probability of animposter achieving 99.89% accuracy for Hand Geometry and 93 % accuracy withFacial Verification based on George's two templates residing on the biometric database. In other words, what is the statistical possibility ofan imposter have facial characteristics that match the facial template onthe database by a similarity level of 97% and that the same imposter has hand geometry that matches that on the database by an accuracy level of 99.89%? Is not the possibility far less than 0.08%, which is our verification threshold on the Hand Geometry reader? What may be required in order to resolve the issues of falsely rejected legitimate users is an algorithm that is weighted in favor of the primary biometric technology and weighs the primary biometrics' rejection level against the secondary's evaluation of how accurately the rejected user matches the secondary biometric template in comparison to the level that he was rejected by the primary biometric technology. The levels of weighing each of the biometrics acceptance/rejection levels will be subjective and based on security requirements.
The following is an outline of Josef Kittle's paper at the Biometric Conference in Hong Kong. http://www.wave-report.com/other-html-files/currentwave.htm ****ICBA 2004, First International Conference on Biometric Authentication By John LattaHong Kong, July 15 - 17, 2004 Challenge of Biometric Fusion Josef Kittle, University of Surrey, UK, gave a keynote presentation on"Fusion of Intramodal and Multimodal Biometric Experts." It was one of themost interesting of the conference. One example in facial recognition wasbased on color channels. Three different methods related to the color channels netted TER, total error rates, of 5.8, 5.8 and 4.8. But when combined using a fusion process, the TER dropped to 1.9. This is anintramodal fusion because the same biometric modality was used, i.e., facial. Another example used face, voice and lips for the biometrics. In this case the HTER (1/2 TER) varied from .74 to 13.3. When it was fused andall modalities were used, the HTER dropped to .15. The last example was the fusion of face and voice with the HTER of 1.8 and 1.23. But the fused HTER was only .28. Logic draws us to the expectation that the use of more than one and even multiple biometric measures would result in lower error rates. Professor Kittle showed that the real challenge comes in operational environments. In these environments: Not all sensors are assumed to be able to collect their respective biometric for every individual in the authentication/identification process, The potential for fusion is limited to the number of biometrics used at the time of enrollment, and Some biometrics are of higher reliability that others. Operational expectations are that the use of biometrics will force the evaluation in the direction of the biometric with the highest confidence. Note that this is the case with Hong Kong Immigration which has both fingerprints and images. The images are not used as a biometric. In fusion, we would expect that the weights applied to the sensors used for authentication/ identification should be based on the reliability of the biometric. The WAVE asked the question: How does one compensate for these issues in operational environments? In response, it was stated this is oneof the issues to be addressed in the R&D of multimodal systems. The promise of fusion also carries with it the need for more research.What is of interest here is that in theory there is no improvement possibleby layering, combining or fusing two or more biometrics, yet in practice the test results indicate something else.
Yona Flink
OptiSec Ltd. Israel yona@optisec-systems.com
Mobile: +972 54 430 8727
Saturday, July 31, 2004
COMPARING PASSWORDS ....
Abstract
For decades, the password has been the standard means for user authentication on computers. However, as users are required to remember more, longer, and changing passwords, it is evident that a more convenient and secure solution to user authentication is necessary. This paper examines passwords, security tokens, and biometrics – which we collectively call authenticators – and compares these authenticators and their combinations. We examine effectiveness against several attacks and suitability for particular security specifications such as compromise detection and non-repudiation. Examples of authenticator combinations and protocols are described to show tradeoffs and solutions that meet chosen, practical requirements. The paper endeavors to offer a comprehensive picture of user authentication solutions for the purposes of evaluating options for use and identifying deficiencies requiring further research.
Wednesday, June 23, 2004
TOWARDS PRIVACY ENHANCING APPLICATIONS OF BIOMETRICS
C.M. Most, “Towards Privacy Enhancing Applications of Biometrics”, DIGITAL ID WORLD June/July 2004.
URL: http://magazine.digitalidworld.com/Jun04/Page18.pdf
Friday, May 21, 2004
NEW SECURITY DEVICE A HANDY WAY TO STOP CREDIT CARD FRAUD
By Harold Lee
DAILY BRUIN REPORTER
hlee@media.ucla.edu
A team of UCLA graduate student researchers is working to eliminate a variety of security and privacy problems by creating a portable device that would identify users by their thumbprints.
BIOMETRICS 2004
http://www.biometrics-2004.com